A BadUSB can hack a computer in a matter of seconds, but how is that even possible? Let's explore this fascinating topic.
Learn about BadUSB hacking in my online course at learnbadusb.com
What is a BadUSB

On the outside, a BadUSB is often indistinguishable from a regular flash drive or USB cable. But on the inside is a chip programmed to act as a USB keyboard, so it can open a terminal and run commands to hijack the computer in a matter of seconds.
BadUSBs work because they abuse our expectations and trust towards USB cables and flash drives. But they are also using the computer's trust in USB keyboards.
Keyboard input is trusted because it comes from humans, and humans have full access to the computer. The problem is that the computer doesn't know if the keystrokes it receives come from an actual human or just another computer.
Keystroke Injection Attack
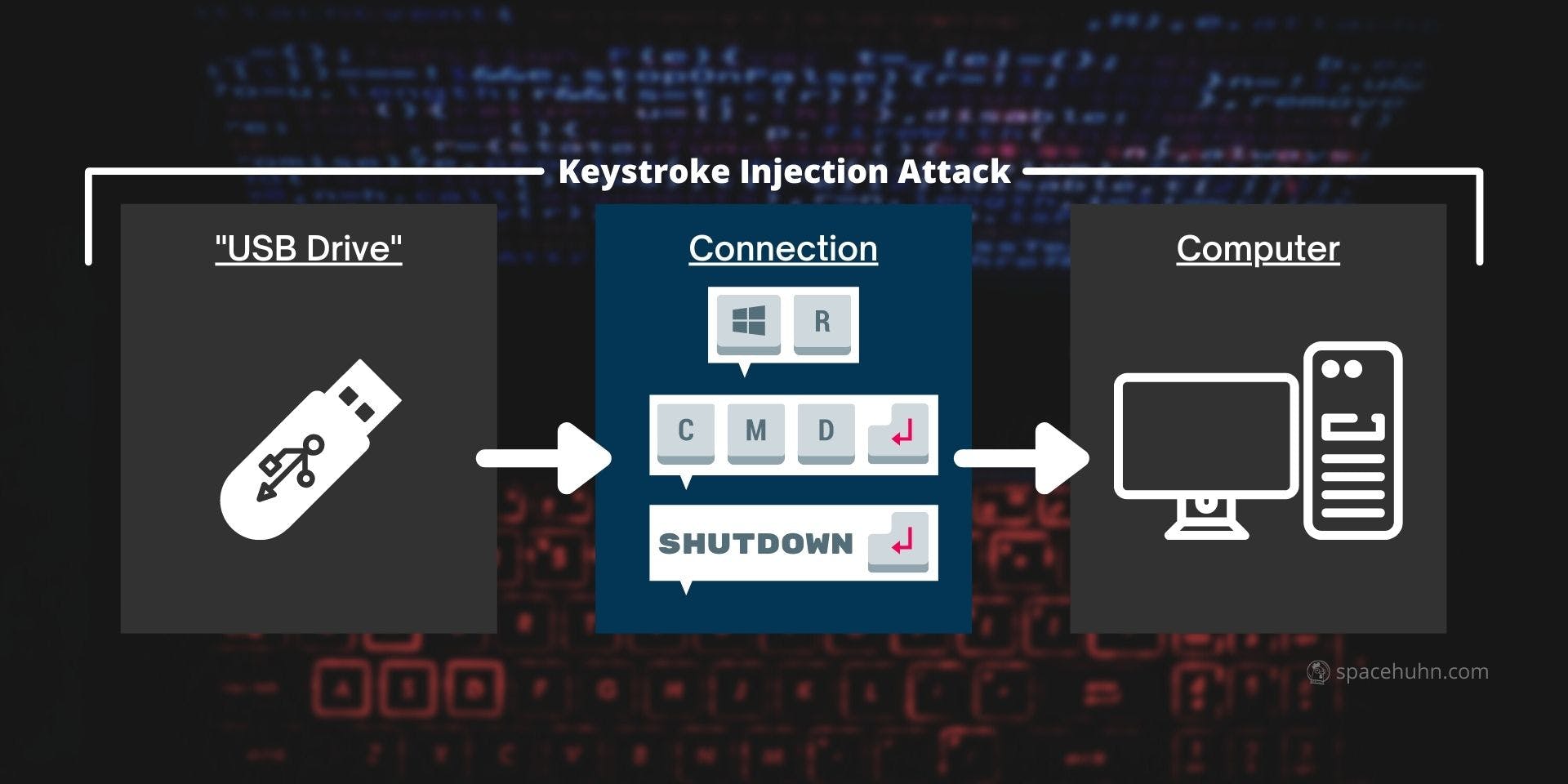
BadUSBs are programmed to perform keystroke injection attacks by sending a sequence of keystrokes to the computer. The computer, however, thinks a human typed those and will handle them as such, even though the BadUSB injects them at incredible speeds (over 9000 characters per second).
Depending on the keystroke sequence sent, a BadUSB can install malware or exfiltrate private data. It can do almost everything you can do on your computer right now.
Limitations

While BadUSBs can be very scary, they are not all-powerful.
They always require physical access to the target device (and their USB ports). For example, someone needs to have access to your computer to plug in a malicious USB device. Or the attacker has to make you plug it in for them. This is why you should never just plug in an unknown USB device!
In most cases, it is also required that the target computer is already running and unlocked. That's because most BadUSBs are 'dumb' and just blindly send keystrokes according to their programming. So they can not detect if they are stuck in a password prompt. This is why you should always lock your computer!
BadUSB Course
If this sparked your interest in BadUSBs and you want to know more, I got you covered! 👉 Visit learnbadusb.com to get access to my new online course about BadUSBs!
It teaches you everything you have to know about BadUSBs - including how to build one yourself! It's beginner-friendly and a great way to get started with ethical hacking.